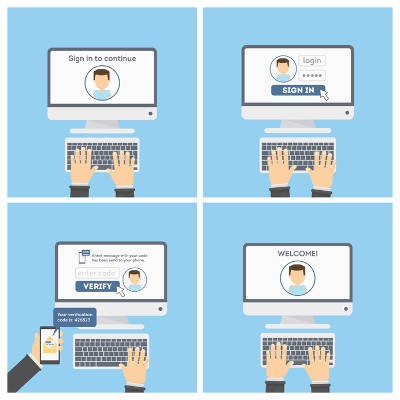
I want to start this article out by admitting that there are a lot of active threats out there these days. There are hackers--hacking collectives, actually--that’s whole purpose is to infiltrate businesses and steal data, money, and most often, the trust people have in their technology. One way to help keep your stuff secure is by relying on two-factor authentication.
FRS Pros Blog
Whether you love, hate, or are just indifferent about Facebook (no judgement here), it’s worth configuring and locking down your account to control what others can see about you.
Facebook is front and center when it comes to privacy-related issues worldwide, so in this blog we are going to discuss how you can take control of your personal information. This post will also serve as an excellent starting point for anyone who doesn’t understand 2-factor authentication.
As smartphones have become smarter, they have become filled with more and more data that needs to be kept private for the owner’s safety and security. This is why it is fortunate that there are also more ways to secure a smartphone against unauthorized use. We’ll examine the many options to devise which is the most secure.
2018 could potentially be a big year for your business. However, your business needs to be around long enough to see any positives that may come its way, which means you need to be prepared for the negatives. Here are five resolutions for you to make this year to help preserve your organization’s cybersecurity.
Data security has to be a core consideration of the modern business, so every small effort you can take to protect your business is important. One such effort is the implementation of two-factor authentication. However, your employees may not initially feel entirely comfortable with some facets of two-factor authentication.